Does Your IC Security Need a Renovation?
What do you want to protect? How will you protect it? What do you stand to lose if you don’t?
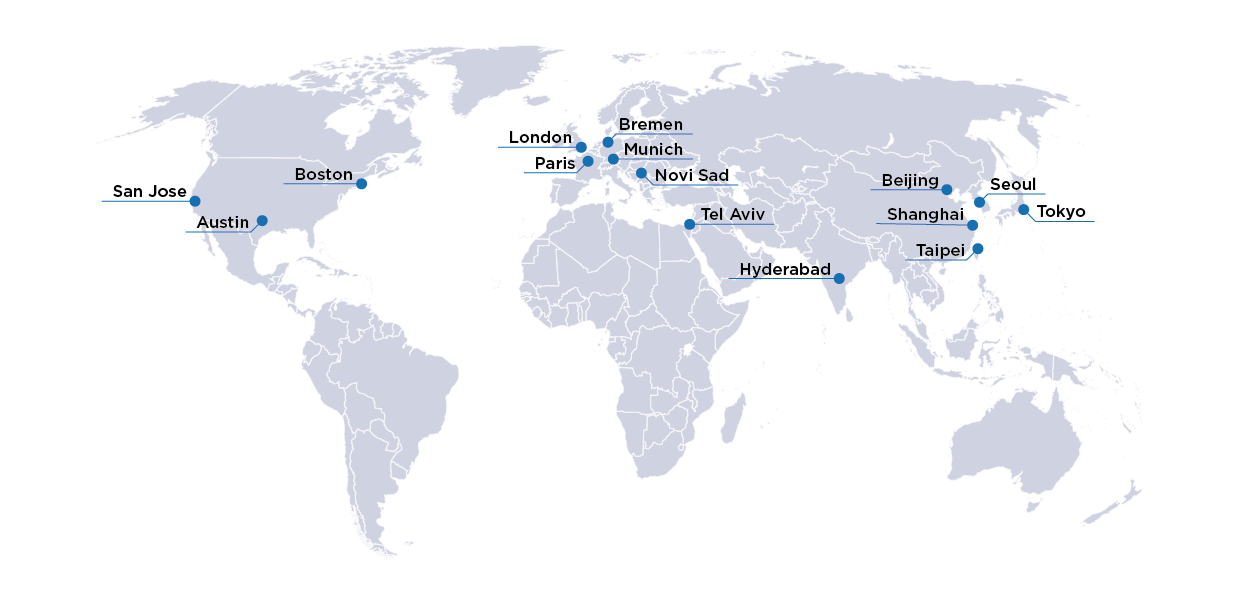
By McKenzie Ross, Director Corporate Marketing, OneSpin: A Siemens Business
Five years ago, I moved from Silicon Valley to Gig Harbor, Washington and bought a fixer-upper. As part of my ongoing (and extensive) home renovations, I just finished having the entire exterior redone: roof, siding, paint, masonry, front porch, back deck, outdoor lighting … the works. If you’ve ever embarked on any kind of home remodel project, I don’t have to tell you that the process included pain: construction always takes longer and costs more than anticipated. On the positive side, however, it felt good to undo the errors and neglect of the previous owners, achieve the look and style that I wanted, increase the value of my property, and ensure that I will be well sheltered from the elements for years to come.

Because the renovation was invasive—it’s not every day that you effectively peel your home like a hardboiled egg—I had a unique opportunity to augment my home security while the exterior of the house was down to the studs and access was comparatively easy. But how much security did I really need, and what would it cost? For context, I live in a fairly small town with a low crime rate. I’m located at the end of a quiet, private cul-de-sac in a rural setting. I know my neighbors well, and three of the four nearest ones are retired and almost always home. We look out for each other. In short, I already had lots of reasons to feel safe. On the other hand, I value my safety, and I have certain belongings, like family heirlooms, that I consider irreplaceable. I liked the idea of having the extra peace of mind that a home security system could provide. But there are so many out there! Alarms, cameras, motion sensors, automatic lights, monitoring, video archiving … there was a lot to think about.
Serendipitously, my remodel project coincided with a recent webinar given by my colleague, John Hallman, OneSpin’s product manager for trust and security. In “How to Start Securing Your IC,” which is now available on demand, John offers a two-part crash course on IC security. I’m by no means technical, but the webinar ended up inspiring me to take a proactive approach my own security conundrum, so I’d like to summarize the content for you here, and I encourage you to watch the full videos at your convenience.
In Section 1: Introduction to Trust and Security Fundamentals, John sets the scene for what’s happening in IC security today. There’s some scary stuff out there! SolarWinds. Spectre. Meltdown. On the heels of recent high-profile cyberattacks, some of which have affected critical infrastructure, the electronics industry has come to the resounding consensus that security is of paramount importance in all areas of IC design. Unfortunately, aligning our views was the easy part.
The “how” of securing an integrated circuit is complex. As John notes, trust and security is a huge space; even knowing where to find reliable information to get started can be daunting. Engineers are faced with wading through the vast amounts of hardware security materials out there. They must prioritize their security needs to address the most pressing and safeguard against threats, which can take myriad forms. Lastly, if they truly hope to give security its due, engineers may ultimately need to modify their design methodology and verification flow to have security in mind from start to finish.
Rounding out the context that John offers in the first part of the webinar are:
- Definitions of essential security terminology
- Background information on industry standards, including ISO/SAE 21434 and Accellera SA-EDI
- An overview of known hardware weaknesses and Common Weakness Enumeration
These provide a firm foundation for the second half of the webinar, which offers a closer look at trust and security verification in action.
In Section 2: Getting Started with OneSpin for Trust and Security, John delves into the strengths of formal verification for trust and security, including its distinction as the only verification technology that can to prove the absence of something (e.g., a Trojan) from a design. Formal also offers a systematic, mathematical approach to verifying that a design is free of weaknesses. John digs into how effective it is to have security baked into a verification plan, taking a closer look at Solar Winds as a practical example and cautionary tale. He closes by highlighting how OneSpin can help you lay a foundation of functional correctness in your IC design and layer security verification atop that to achieve your trust and security goals. With automated apps harnessing the power of formal verification and experts ready to help you, OneSpin can make the challenging task of securing your IC a lot easier.
John’s webinar highlighted to me that, though they may seem very different on the surface, IC security and home security actually have a lot in common, to the point that each can be a metaphor for the other. Home security is something we all want, but it’s not always clear how much we need. It can also be pricey and challenging to implement. There are up-front costs to get it in place, plus ongoing fees, like security system monitoring and cloud video archiving, both of which can seem a little steep—that is, until you compare those costs with the potential losses you might suffer in a burglary, or contemplate the nightmare of falling victim to a home invasion robbery. It’s easiest if you design and build a house that already includes security systems, because retrofitting to add things like alarms and cameras is invasive and messy. We can’t all build a brand-new house, however. Remodeling to add security measures might be inconvenient, but it’s definitely better than going without.
Similarly, securing your chip is easier if you start with security in mind and keep it in focus every step of the way through design and verification—but if you haven’t been paying much attention to IC security thus far, there’s no time like the present to start. It will take some investment and effort, and maybe even a complete remodel of your design and verification methodology … but it’s certainly a lot better than falling victim to an attack.
Ultimately, security boils down to asking yourself: What do you want to protect? How will you protect it? What do you stand to lose if you don’t? I went ahead and had that home security system installed, and I’m paying for the monitoring and video archiving. Maybe it’s just my imagination, but it feels like I’m sleeping a little more soundly already.